| Developer(s) | Carl-Fredrik Neikter |
|---|---|
| Stable release | |
| Operating system | Microsoft Windows, UNIX-systems (v1.60 client only) |
| Type | Remote administration |
| License | Shareware |
| Website | www.tcp-ip-info.de/trojaner_und_viren/netbus_pro_eng.htm |
- Netbus backdoor is an illegal tool to gain access to a server or computer bypassing the security mechanisms of the system. Typically, attackers create a backdoors to gain access to the operating system to perform various actions. This can be stealing passwords and credit card numbers (aka spyware), installing ransomware, or cryptocurrency miners.
- Netbus client (v1.70) works fine in Windows 2000 and in Windows XP as well. Major parts of the protocol, used between the client and server interaction (in version 1.70) are textual. Thus the server can be controlled by typing human understandable commands over a raw TCP connection.
- Following is the stepwise procedure for installation and configuration of NetBus 2.0 Pro (server and client). 1) Download NetBus 2.0 Pro. From here – NB2ProBeta.zip. 2) Extract and install properly on your system. 3) After installation you will find the two shortcuts in the NetBus installation directory.
After each kill, try connecting to port 12345 and when that fails, the last task killed was the NetBus server. Next prevent NetBus from being started at boot time. Delete the registry key HKEYLOCALMACHINE SOFTWARE Microsoft Windows CurrentVersion Run XXX, where XXX is the name of the NetBus server. Delete the NetBus server executable.
NetBus or Netbus is a software program for remotely controlling a Microsoft Windows computer system over a network. It was created in 1998 and has been very controversial for its potential of being used as a trojan horse.[1][2]
NetBus was written in Delphi by Carl-Fredrik Neikter, a Swedish programmer in March 1998. It was in wide circulation before Back Orifice was released, in August 1998. The author claimed that the program was meant to be used for pranks, not for illegally breaking into computer systems. Translated from Swedish, the name means 'NetPrank'.
However, use of NetBus has had serious consequences. In 1999, NetBus was used to plant child pornography on the work computer of a law scholar at Lund University. The 3,500 images were discovered by system administrators, and the law scholar was assumed to have downloaded them knowingly. He lost his research position at the faculty, and following the publication of his name fled the country and had to seek professional medical care to cope with the stress. He was acquitted from criminal charges in late 2004, as a court found that NetBus had been used to control his computer.[3]
There are two components to the client–server architecture. The server must be installed and run on the computer that should be remotely controlled. It was an .exe file with a file size of almost 500 KB. The name and icon varied a lot from version to version. Common names were 'Patch.exe' and 'SysEdit.exe'. When started for the first time, the server would install itself on the host computer, including modifying the Windows registry so that it starts automatically on each system startup. The server is a faceless process listening for connections on port 12345 (in some versions, the port number can be adjusted). Port 12346 is used for some tasks, as well as port 20034.
The client was a separate program presenting a graphical user interface that allowed the user to perform a number of activities on the remote computer. Examples of its capabilities:
- Keystroke injection
- Screen captures
- Program launching
- File browsing
- Shutting down the system
- Opening / closing CD-tray
- Tunneling protocol (NetBus connections through a number of systems.)
The NetBus client was designed to support the following operating system versions:
Netbus client (v1.70) works fine in Windows 2000 and in Windows XP as well. Major parts of the protocol, used between the client and server interaction (in version 1.70) are textual. Thus the server can be controlled by typing human understandable commands over a raw TCP connection. It is more difficult than using the client application yet allows one to administrate computers with NetBus from operating environments other than Windows, or when original client is not available. Features (such as screen capture) require an application with ability of accepting binary data, such as netcat. Most of more common protocols (like the Internet Relay Chat protocol, POP3SMTP, HTTP) can also be used over a raw connections in a similar way.
NetBus 2.0 Pro was released in February 1999. It was marketed commercially as a powerful remote administration tool. It was less stealthy, but special hacked versions exist that make it possible to use it for illegal purposes.
Netbus 2 0 Server And Client Software List
All versions of the program were widely used by 'script kiddies' and was popularized by the release of Back Orifice. Because of its smaller size, Back Orifice can be used to gain some access to a machine. The attacker can then use Back Orifice to install the NetBus server on the target computer. Most anti-virus programs detect and remove NetBus.
References
- ^Kulakow, Seth (2001). 'NetBus 2.1, Is It Still a Trojan Horse or an Actual Valid Remote Control Administration Tool?'. SANS Institute: Reading Room - Malicious Code. Retrieved 2020-03-26.
- ^William (Chuck) Easttom II (18 October 2013). Network Defense and Countermeasures: Principles and Practices. Pearson Education. pp. 262–. ISBN978-0-13-338438-3.
- ^'Offer för porrkupp' (in Swedish). Expressen. November 28, 2004. Archived from the original on June 21, 2009. Retrieved May 31, 2007.
External links
- Information about NetBus — Information from anti-virus vendor F-Secure.
- lxnb — A NetBUS client for Linux that works with NetBus 1.60.
- NIL — NIL 0.1b - NIL is a simple Netbus client with a clean interface for Linux.
 It is capable of :--
It is capable of :--* Open/Close CD-ROM
* Show optional BMP/JPG image
* Swap mouse buttons
* Start optional application
* Play a wav file
* Control mouse
* Show different kind's of messages
* Shut down Windows
* Download/Upload/Delete files
* Go to an optional URL
* Send keystrokes and disable keys
* Listen for and send keystrokes
* Take a screendump
* Increase and decrease the sound-volume
* Record sounds from the microphone
* Make click sounds every time a key is pressed
This utility also has the ability to scan 'Class C' addresses by adding '+Number of ports' to the end of the target address. Example: 255.255.255.1+254 will scan 255.255.255.1 through 255.
NetBus 2.0 Pro :- It was completely re-written and re-designed. It now has increased features such as improved GUI for client and server, improved file manager, windows manager, registry manager, plugin manager, capture of web cam images, n...more............!
Following is the stepwise procedure for installation and configuration of NetBus 2.0 Pro (server and client).
1) Download NetBus 2.0 Pro. from here - NB2ProBeta.zip
2) Extract and install properly on your system.
3) After installation you will find the two shortcuts in the NetBus installation directory.

This is to be executed on victim's system.
This is to be executed on your system.
4) By Executing the 'NetBus Server' (on victim's computer), you will be greeted by a window as shown in figure (left). Click on 'Settings' button.
Here you can configure server settings such as port no, password, visibility, auto/manual start, etc. as shown in figure (right).
Click on 'OK' button to finish NetBus Server settings.
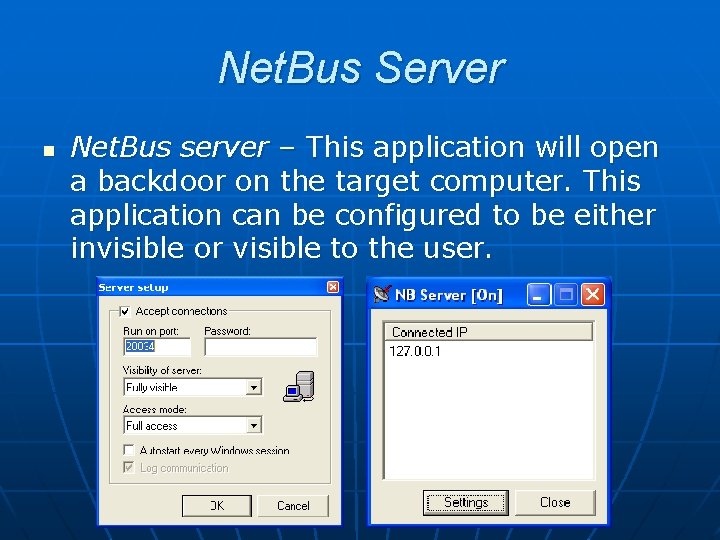
Then close the NetBus Server window.
5) By executing 'NetBus' (i.e. client)(on your system), you will be greeted by a window as shown below-
6) To add a new host go to the menu 'Host' and then click 'New'. This is as shown in figure (left).
Here you should enter the proper Destination(e.g. 'My Computer'), IP Address(eg. 72.232.50.186), TCP Port(by default 20034), Username/Password(exactly same as that of 'NetBus Server') for target computer.
Click on 'OK' to finish the addition of new host.
Netbus 2 0 Server And Client Software
7) Now you are ready to connect with target(victim's) computer.To do so, select the host from main window then go to 'Host' menu and then click 'Connect'.
8) After client get connected with server(target computer), you can use any of the features of 'NetBus Trojan' as listed above. You can see all these tools on 'Toolbar' of NetBus Client.



